A strong cybersecurity stance is a key defence against malicious cyber attacks. It’s imperative to understand the right cybersecurity measures are the only way to protect your organisation. Together with the most expert partners, Sun Evo Tech brings to our clients new innovative services. We are commited in empowering and protecting your business on its most reliable way, collaborating with leaders in cybersecurity solutions.
Cybersecurity
Cybersecurity is a shared responsibility: The more systems we secure, the more secure we all are. – Jeh Johnson
DigitalSkills.
Along with DigitalSkills, we deliver cybersecurity solutions on the market, helping companies to increase their cyber resilience and protect assets, systems, data and professionals. From conducting automated penetration tests; tracking and protecting organization’s sensitive data; improving the log in systems with biometric access controls; protecting corporate assets and systems by installing electronic certificates; protecting mobile devices and all IoT devices; to advanced cyber security train programs, we offer you have fundamental solutions to increase the cybersecurity of your company.
Automated Penetration Testing
We provide an Automated self-learning Penetration Testing Platform, modelling hackers’ thinking process into machine language. The software eliminates the need to perform these tests manually and decreases costs by creating effective virtual hacker opponent that constantly test the organizational infrastructure in new ways to find real exploitation and weak points to provide prioritized remediation options with meaningful reports and alerts, where everything is automatic and real-time. The solution correlates events based on concepts of “machine learning” and “artificial intelligence” demonstrating the true impact for the business of the real vectors of attack.
Mitigation Cellular Cyber Risks on connected devices
Our FirstPoint solution offers the market’s first and only protection against fake cell towers (aka “IMSI catchers”) and other network vulnerabilities, blocking snooping of your devices’ voice, SMS, data, and location information, as well as preventing the insertion of malware, by anonymizing your device’s identity. This solution is designed to not require agents, without fail, protecting mobile devices at the level of the network provider itself since it analyzes the signal and does not allow any malicious access (available for networks from 2G to 5G). It does not cause latency or disruption of service.
Secure Microsoft 365 Backup & Advanced Threat Protection
Datto Saas Protection+ is a comprehensive backup and recovery solution for Microsoft 365 with integrated advanced threat protection.SaaS Protection+ is both SaaS Protection plus SaaS Defense, which scans Microsoft 365 for cyber threats and backs up 3x daily. Comprehensive detection, protection, and recovery helps you safeguard your clients´ Microsoft 365 data against both known and unknown cyber threats and common data loss scenarios.
All you need to protect your assets and Airspace from IoT attacks
Harmony IoT accurately identifies vulnerabilities and threats from smart-connected devices that are active in your environment. It prevents malicious IoT activity and policy violations, in real time, to keep your business protected. Harmony IoT allows you to embrace IoT and wireless devices, giving you an enterprise-grade defence that quickly and easily identifies, monitors, and protects all the smart-connected devices operating in and around your business. With Harmony IoT, you know exactly what is happening and can protect your critical assets from IoT and wireless attacks.
Detection, warning, and prevention of cyber threats on Physical Security and Control System networks
Nelysis is a global leader of cyber security solutions for Physical Security and Control Systems networks. Nelysis offers innovative solutions, a critical layer of cyber security, to protect network infrastructure and assets. Nelysis’s Vanguard solution provides a complete solution to reduce risk created by external and insider attackers while minimizing operational downtime.
 | Solutions.
| Solutions.
Kaspersky Lab’s deep threat intelligence and security expertise is constantly transforming into next generation security solutions and services to protect businesses, critical infrastructure, governments and consumers around the globe.
As the world has become more digitized and globalized, Kaspersky has become a technology leader with an advanced and comprehensive portfolio of security solutions and services.
Interested in improving the security of your business with Kaspersky Cybersecurity Solutions?
 | Solutions.
| Solutions.
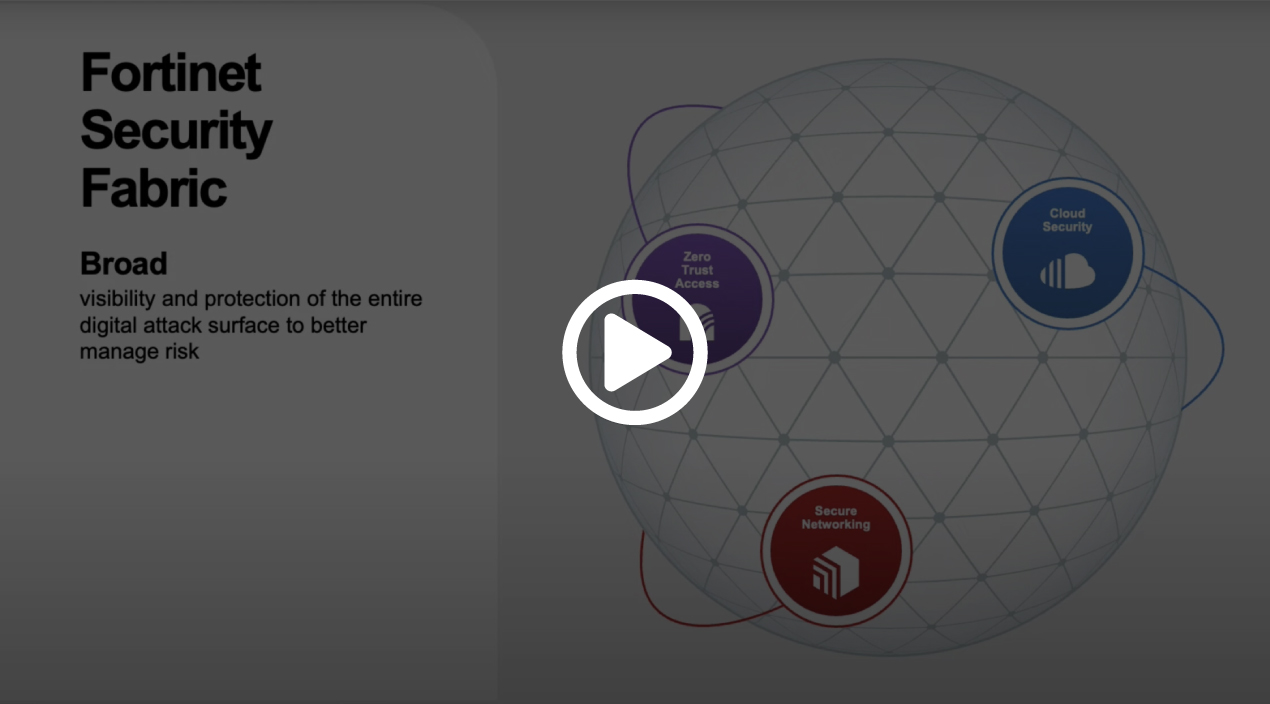
Fortinet makes possible a digital world that we can always trust through its mission to protect people, devices, and data everywhere. The Fortinet Security Fabric platform delivers broad, integrated, and automated protections across the entire digital attack surface, securing critical devices, data, applications, and connections from the data center to the cloud to the home office.
The Security Fabric enables organizations to achieve their digital innovations outcomes without compromise by delivering a true cybersecurity platform that provides:
- Broad visibility and protection of the entire digital attack surface to better manage risk
- Integrated solutions that reduce management complexity and share threat intelligence
- Automated self-healing networks with Al-driven security for fast and efficient operations





 | Solutions.
| Solutions.